FILTER
soc 2
What is SOC 2? Everything You Need to Know.
In today’s market, SOC 2 has become table steaks. It’s necessary to provide security assurance to...
READ MORE

Security Controls, Explained: Logging and Monitoring
Control of the Month: Logging and Monitoring Security Events This article is part of our Control of the Month...
READ MORE
The Top 5 Information Security Tasks Nobody Likes Doing
And How To Make Them Easier, With or Without Compliance Automation There are a lot of steps in creating an...
READ MORE

SOC 2 vs HIPAA Compliance: What’s the Difference?
Everyone feels the pressure to level up their data security game but what’s the difference between SOC...
READ MORE

The Best SOC 2 Compliance Checklist: What We Learned Passing SOC 2 Type 2
We learned so much passing SOC 2 Type 2 that we compiled it into the best SOC 2 compliance checklist! SOC 2...
READ MORE

Secrets to Selecting the Right SOC 2 Vendor
In this article, we condense unbiased, expert research from Fractional CISO highlighting: Three core SOC 2...
READ MORE

What Can and Can’t Be Automated for SOC 2
Everyone is searching for a simplified SOC 2 experience but there’s some confusion about what can and...
READ MORE

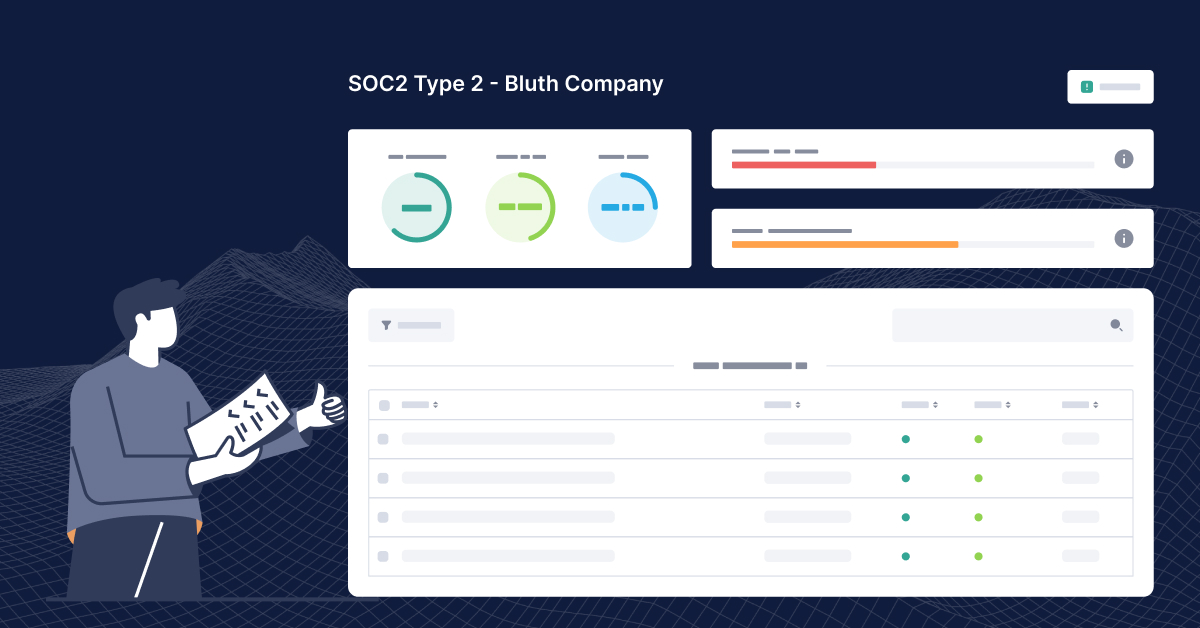
SOC 2 Bootcamp Part 2: Policies and Controls
Welcome to part two of SOC 2 Bootcamp coving policies and controls! Quick refresher—we borrowed Bluth...
READ MORE

Sorry, SOC 2 in 14 Days Is Too Good to Be True
You’re in a cold sweat. A customer or prospect needed you to be SOC 2 compliant yesterday. But...
READ MORE
SOC 2 Bootcamp Part 1: Scoping and Auditor Selection
You probably have customers asking you all the time if you’re SOC 2 compliant. You’re not yet,...
READ MORE

A SOC 2 Report Example
Have you seen a SOC 2 report example before? Well, now you can say that you have! Today, we’re going...
READ MORE

How Long Does SOC 2 Compliance Take?
One of the most common questions we hear is: “How long does it take to get SOC 2?” See, SOC 2 isn’t...
READ MORE