FILTER
The Full Scope
Trends, tips, regulations, and all things security
The Importance of a PCI DSS Self-Assessment Questionnaire
You’re a busy and important person, with many plates to spin and deals to win. I get that!...
READ MORE
Tips and Tricks for Enterprise IT Risk Assessments
Did you know that 76% of enterprises lack a clearly defined enterprise IT risk assessment and management...
READ MORE
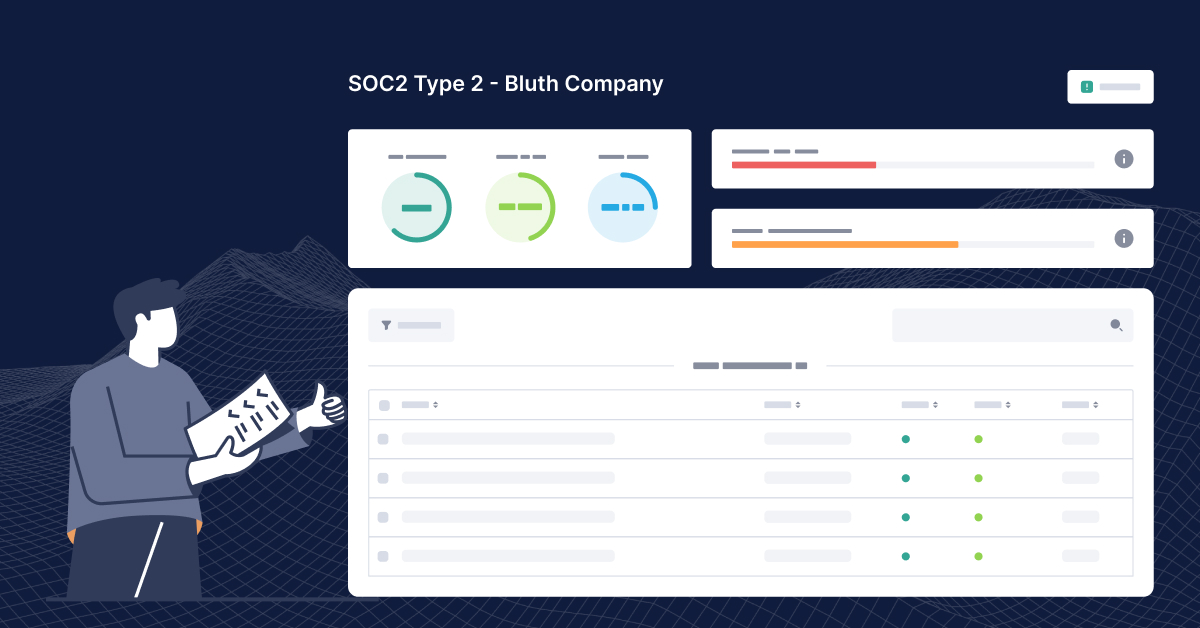
SOC 2 Bootcamp Part 2: Policies and Controls
Welcome to part two of SOC 2 Bootcamp coving policies and controls! Quick refresher—we borrowed Bluth...
READ MORE
How to Perform a Vendor Risk Assessment
Knowing who your vendors are, how they manage their risks and the impact it could have on your company is a...
READ MORE
Introducing the CMMC Framework
Last year, to protect Controlled Unclassified Information and Federal Contract Information, the US Department...
READ MORE
The Basics of a Risk Treatment Plan
A risk treatment plan (RTP) is an essential part of an organization’s InfoSec program. In fact, ISO...
READ MORE
Sorry, SOC 2 in 14 Days Is Too Good to Be True
You’re in a cold sweat. A customer or prospect needed you to be SOC 2 compliant yesterday. But...
READ MORE
SOC 2 Bootcamp Part 1: Scoping and Auditor Selection
You probably have customers asking you all the time if you’re SOC 2 compliant. You’re not yet,...
READ MORE
Introducing the Tugboat Logic Attestation Report and Certification
Real Security Assurance Takes Real Commitment Being able to demonstrate security compliance can open doors...
READ MORE
SOC 2 Cost Guide
The SOC 2 cost guide has been our most popular download every month since it was first released. It’s...
READ MORE
Tugboat Logic Celebrates Pride
Tugboat Logic is committed to diversity and inclusion, and we want to acknowledge and celebrate all the...
READ MORE
The Basics of GDPR Compliance
Boiling the GDPR down to basics sounds too good to be true, but we did it. Doesn’t 2018 seem like a...
READ MORE